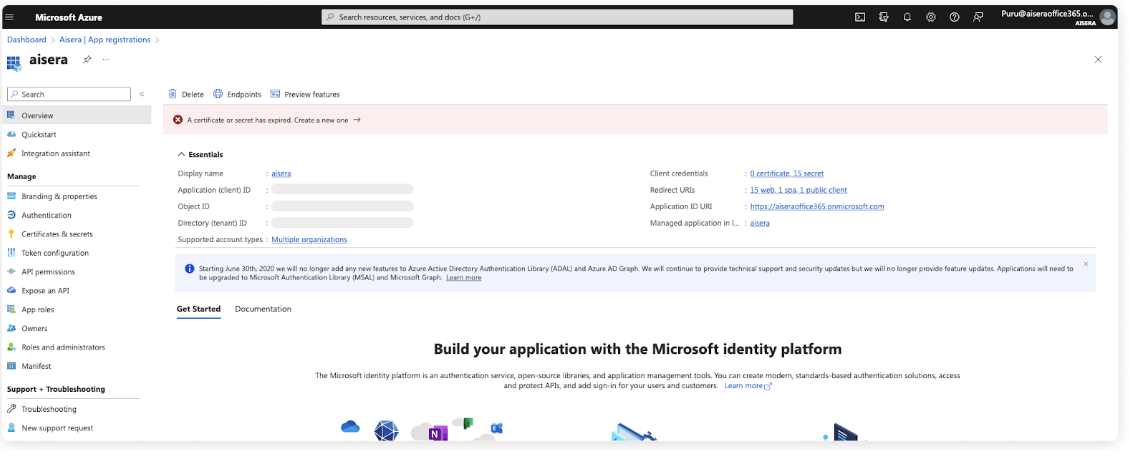
Create a New Azure AD Application
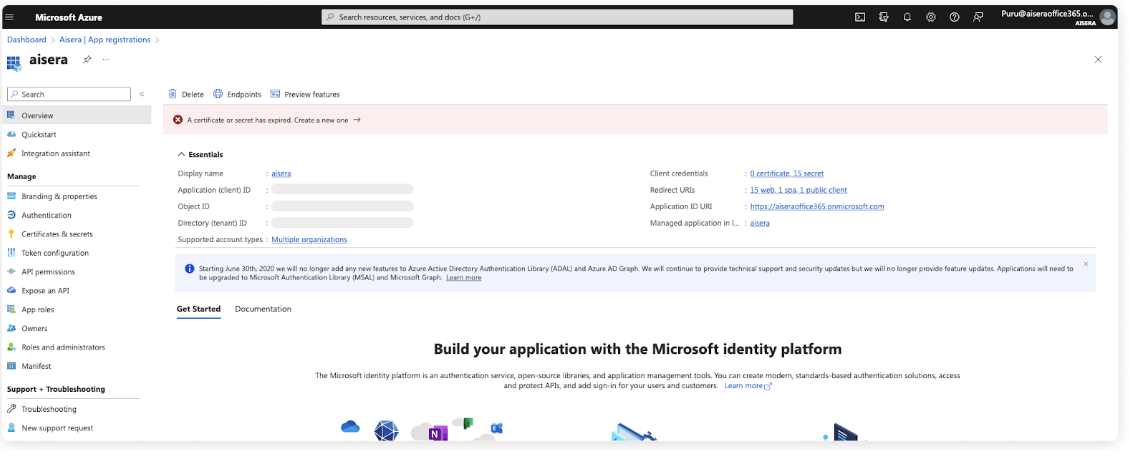
Create a New Azure AD Application

Client ID

Tenant ID

OAuth 2.0 authorization endpoint (v2) & OAuth 2.0 token endpoint (v2)

New Client Secret

Choose the Redirect URL
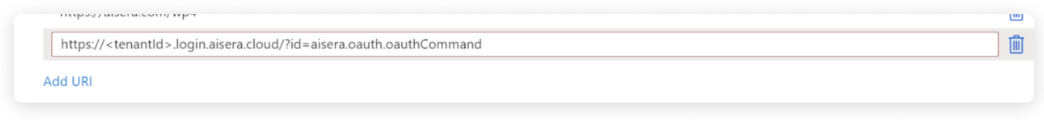
Set the Redirect URL

Assign API Permissions/Token

Set API Read/Write Permissions

Choose Azure Active Directory

Configuration Details - Step 2

Integration Configuration Step 3


